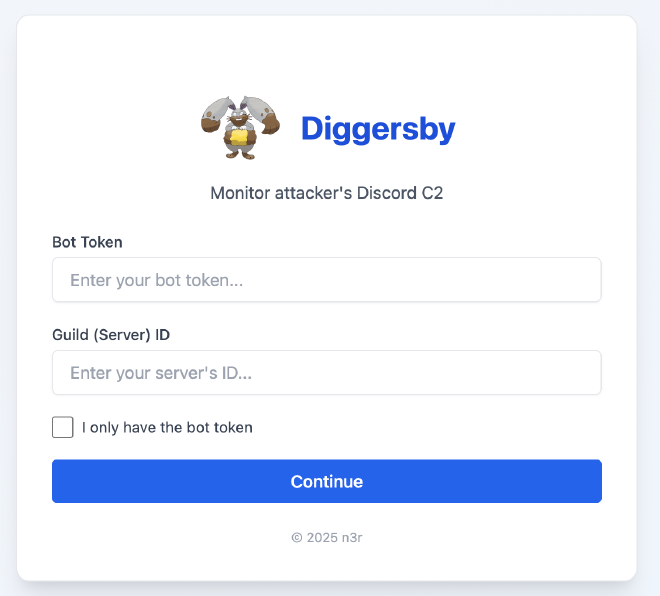
Diggersby, designed to infiltrate and monitor Discord bots that may be employed as command-and-control (C2) channels by malicious actors. By leveraging the Discord Bot API, Diggersby enables users to capture messages from potentially harmful bots, facilitating efficient tracking and analysis.
🔍 Features #
- Monitoring Capabilities:
- Fetch bot name and it’s owner username
- List out all available channels (excluding voice channel)
- Capture messages sent by the bot and users in that channel
⚙️ Usage #
Usage Steps:
- Access https://diggersby.badrulmunir.com/
- Input the bot’s token (e.g., abcdefgh12345!@#$%).
- Enter the server/guild ID if available (e.g., 123456789).
Interfaces #
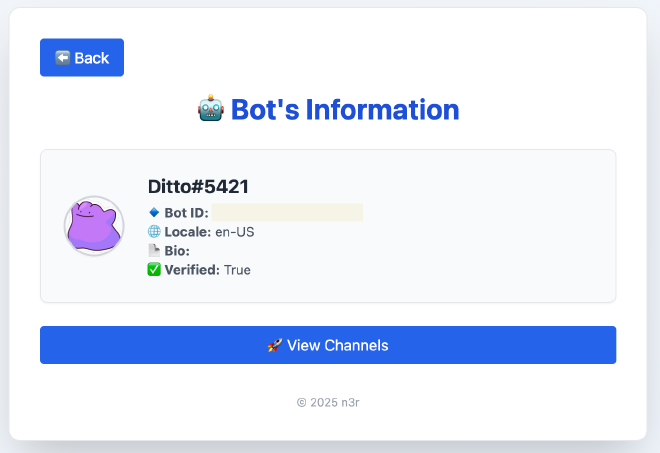
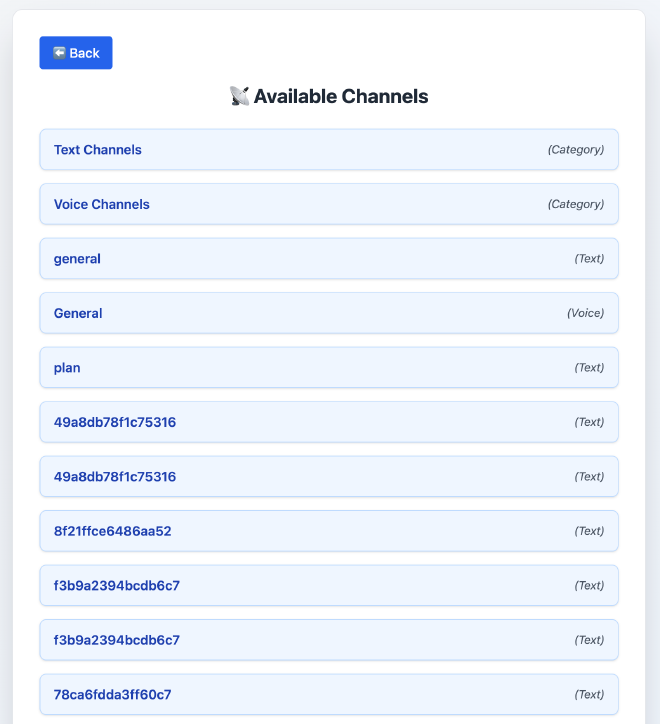
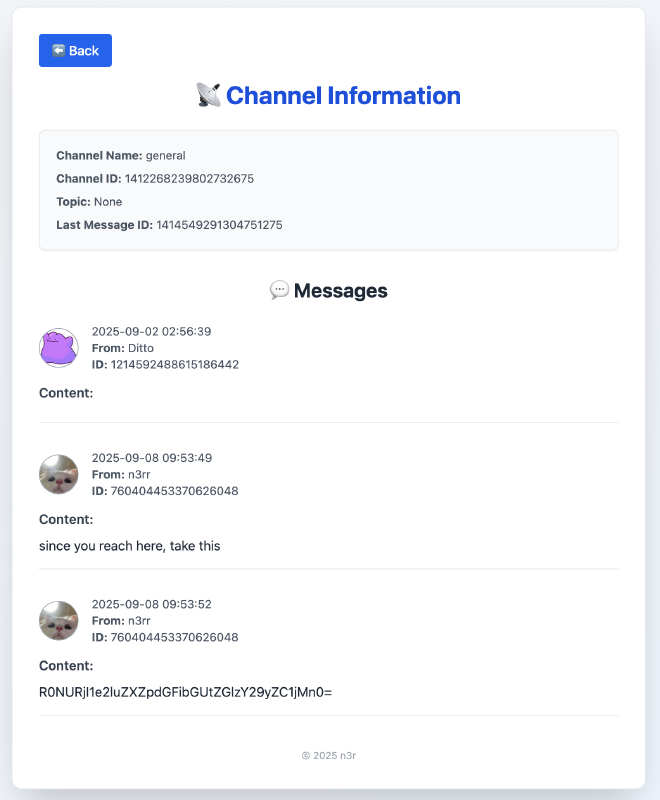
Pictures above are from a Discord Server that i created for a CTF in 2025. The output is only for POC. Can try for yourself.
🛠️ Obtaining Bot Tokens #
- Hunting: Utilize platforms like Fofa to search for exposed tokens.
- Malware Samples: Analyze samples from repositories such as Malware Bazaar to extract tokens.
❌ Limitations #
- This tool only applicaple for Discord Bot that uses Discord API token
- Cannot fetch data from a Discord webhooks (still working on it)
