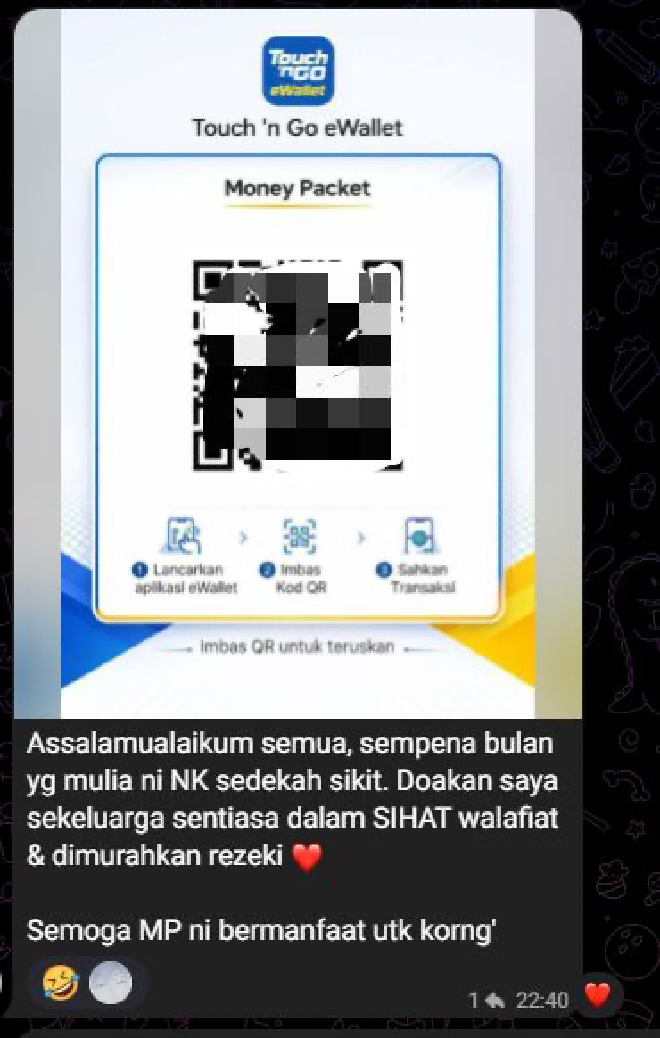
The Bait #
You receive a message — maybe through WhatsApp, Facebook group, or any social media platform. It promises RM500 monthly aid through Touch ’n Go eWallet, supposedly from Jabatan Kebajikan Masyarakat (Malaysia’s Department of Social Welfare).
The URL looks something like:
tng-ewalet2026-vx9.regis-x8.my.id
It looks semi-official. It ends in .my.id. Close enough to .my (Malaysia’s actual domain) to fool most people. But .my.id is actually an Indonesian subdomain registry — cheap, disposable, and easy to register in bulk.
The Landing Page #
Once you scan the QR code or click the the link, you’re greeted with a convincing government-style page:
- Malaysia’s coat of arms prominently displayed
- Official Malay language throughout
- A scrolling ticker of 30+ names — Kaamil bin Haarith, Ibrahim bin Khaalid — all supposedly receiving RM500
None of those people exist. The names are fabricated to create social proof. If dozens of people already received aid, you’d want to register too.
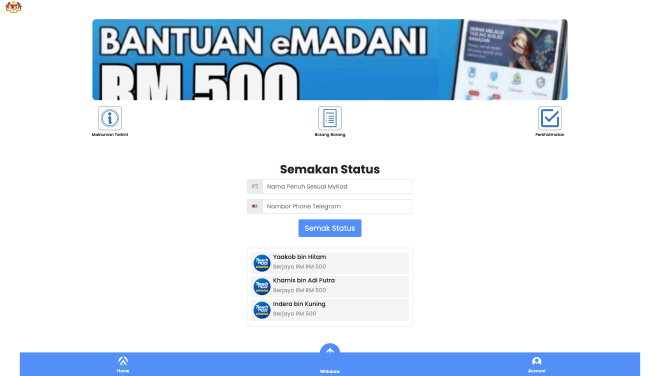
Then there’s a form that ask to put your name and phone number in order to check your “eligibiity”.

This form is rendered at runtime using Vue.js. If a security researcher fetches the page source statically (like I did initially), the form doesn’t exist in the HTML. It only materializes in a live browser. This is deliberate — it keeps the actual data collection invisible to Google Safe Browsing, URL scanners, and most automated analysis tools.
You fill in your name. You fill in your phone number. You hit submit.
This is where it stops being a scam and starts being an attack.
The OTP Relay #
The moment you submit your phone number, it’s sent to the attacker’s backend — likely a Telegram bot or webhook.
The attacker takes your phone number and initiates a real Telegram login on their device. (unconfirm method, but commonly)
Telegram’s authentication system does exactly what it’s designed to do: it sends a one-time password to your phone.
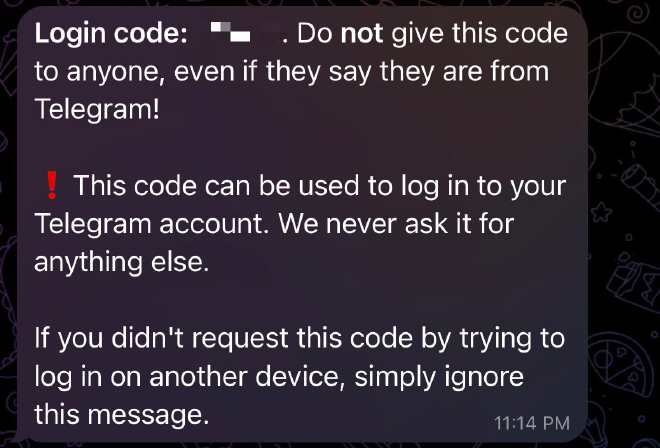
You receive a real code, from the real Telegram, on your real phone.
Back on the phishing page, a new field appears: “Kami telah menghantar kod ke apl Telegram anda.”
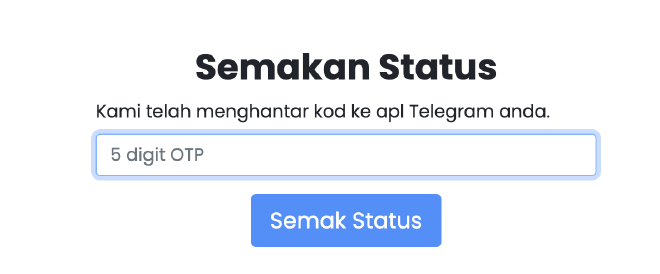
You think it’s part of the aid registration. You enter the code.
The attacker receives it. Completes the Telegram login. Your account is theirs.
Why This Works So Well #
The OTP is legitimate. It comes from Telegram. There’s no spoofed SMS, no sketchy sender name. The victim has no reason to question it — they just submitted their phone number for “government aid” and immediately received a verification code. The timing is perfect.
This is called a real-time OTP relay or man-in-the-middle attack against Telegram’s authentication. The attacker doesn’t need to crack anything. They don’t need malware on your device. They just need you to hand them the key.
Additional Information for Analyst #
Page Title #
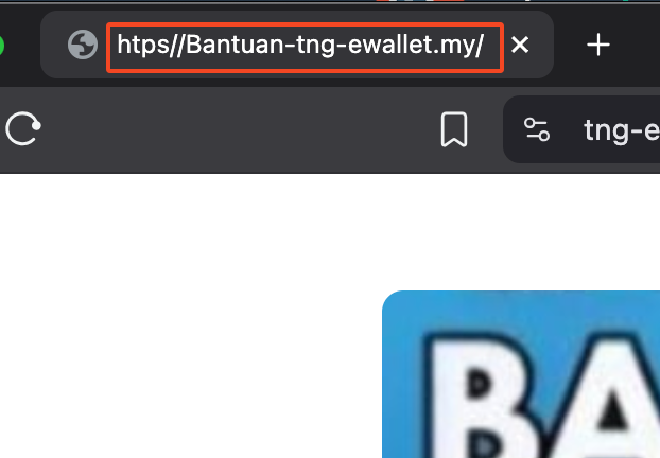
The page title shows htps//Bantuan-tng-ewallet.my/ — visually mimicking a legitimate Malaysian .my domain at a glance.
OTP Form - Broken by design #
var pins = [
500000000000000000000000000000000000, // 36 digits
10000000000000000000000000000000000, // 35 digits
1500000000000000000000000000000000000000000, // 43 digits
];
function submitForm() {
if (pins.includes(+$("#input-pin").val())) {
document.cookie = "pinadded=true;"; // unreachable
} else {
swal("ERROR", "Please Register First", { icon: "error" })
}
}
The keypad only allows single digits. The “valid” PINs are 35–43 digit numbers — physically impossible to enter. Every victim always fails and gets pushed to Telegram. This is intentional, not a bug.
Anti-analysis #
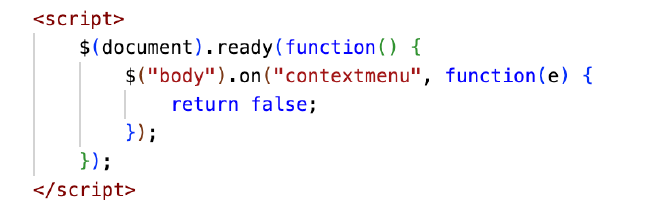
This line of JS disable right click to prevent from opening page source and inspect element. Pain…
Kit Origin — Reused Fraud-as-a-Service Template #
The kit’s JavaScript supports 20+ regional locales (Philippines, Vietnam, Indonesia, Malaysia, Saudi Arabia, Russia, etc.) with Chinese-language internal comments, indicating this is a commercialised fraud template built for multi-country deployment and sold or shared across operators. This operator customised it for Malaysian TNG eWallet targeting.
IOC #
Sha256 #
aea32c34b4c7f43766908856ff2ae7e5c1d75c290eb3b4ae37fb60b9a23c486f index.html
URLs #
hxxps://bantuan-ewallet-tng-my65mo.ask88sx[.]my.id/
hxxps://bantuan-tng-ewallet-my-009k.faj8[.]my.id/
hxxps://new-link-update-nhcr52.dwwb41[.]my.id/
hxxps://tng-ewallet-chc5x7.uncategori-v3[.]my.id/
hxxps://tng-ewallet-ch7v1.qx0-b5[.]my.id/
hxxps://tng-ewallet-xvcy8.fast-x9[.]my.id/
hxxps://tng-ewallet-gxk7v3.zx88c[.]my.id/
hxxps://tbg-ewallet-xdt42.qif7[.]my.id/
hxxps://tng-ewallet-chx9m.axf66[.]my.id/
hxxps://tng-ewallet-ex73f.afc88v[.]my.id/
hxxps://tng-ewallet-chx9m.axf66[.]my.id/
hxxps://tng-digital-bc882x.qx0-b5[.]my.id/
hxxps://tng-ewallet-ex73f.afc88v[.]my.id/
hxxps://bantuan-ewallet-2026.zx88c[.]my.id/
hxxps://tng-digital-cfx008.exc-k7[.]my.id/
hxxps://tng-ewalet2026-vx9.regis-x8[.]my.id/
hxxps://bantuan-tng-ewallet-fj2z8.xxx55[.]my.id/
hxxps://tng-ewallet-ic5s80.zx88[.]my.id/
hxxps://bantuan-tng-ewallet-ckf772f.vip-66dx[.]my.id/
hxxps://bantuan-tng-ewallet-dgp85.saft88[.]my.id/
hxxps://bantuan-ewallet-tng-2025-my76c08.gvw08d[.]my.id/
hxxp://bantuan-ewallet-tng-2025-my76c08.gvw08d[.]my.id/
MITRE ATT&CK Mapping #
| Technique | ID | Evidence |
|---|---|---|
| Phishing: Spearphishing Link | T1566.002 | WhatsApp/SMS lure link |
| Masquerading | T1036 | .my.id spoofing .my; title spoofing |
| Impersonation | T1656 | Fake JKM govt portal, coat of arms |
| Gather Victim Identity Info | T1589 | IC/NRIC, bank, phone via Telegram |
| Credentials from Web Browsers | T1555.003 | PIN harvesting via fake keypad |
| Social Engineering | T1598 | Fake beneficiary list, FOMO, 24h urgency |
| Obfuscated Files or Information | T1027 | Right-click disabled; broken PIN by design |
