Someone is distributing malware disguised as a beta invite for a real indie game. The dropper calls itself CyveraVPN. The package.json buried inside it calls itself a “Beta Of Exonautis.” Exonautis is a legitimate space shooter currently in free demo on Steam, developed by a small studio called BaleYc Studios. The game is real, the studio is real, and neither of them have anything to do with this campaign (afaik).
What they do have is obscurity — real enough to be credible as a beta, unknown enough that a victim can’t easily verify it. That’s the angle.
This post covers the full attack chain: from the fake installer, through two layers of JavaScript obfuscation, to the decrypted GenesisStealer payload underneath. We’ll also look at what makes this campaign trackable — a single builder fingerprint that links several different fake software droppers together. Good for hunting this malware family.
The Sample #
The initial file is CyveraVPN Setup 2.1.1.exe — an 84MB NSIS installer. On execution, it presents a VPN installer UI while silently deploying a Node.js/Electron application containing the actual malware.
| Field | Value |
|---|---|
| Filename | CyveraVPN Setup 2.1.1.exe |
| Size | 88,745,878 bytes (84.6 MB) |
| SHA256 | d24dbda069525134f94904f7a16dbf275abcc0c8d7b0b9c065f39d91d3e2dd7a |
| MD5 | 09cf1fddb08051f5be72245b00638358 |
| Type | PE32 — Nullsoft NSIS Installer (zlib, solid) |
| Imphash | b34f154ec913d2d2c435cbd644e91687 |
Stage 1: The Installer #
NSIS installers are essentially self-extracting archives. Cracking this one open with 7z reveals the structure:
CyveraVPN Setup 2.1.1.exe
└── $PLUGINSDIR/
├── app-64.7z ← main payload archive (87MB)
│ └── resources/
│ ├── app.asar ← Electron app bundle
│ └── app.asar.unpacked/node_modules/
│ ├── better-sqlite3/
│ ├── @primno/dpapi/
│ └── sqlite3/
├── SpiderBanner.dll
├── StdUtils.dll
├── System.dll
└── nsis7z.dll
The app-64.7z archive contains a bundled Electron app — Node.js runtime included. The entry point is defined in package.json extracted from app.asar:
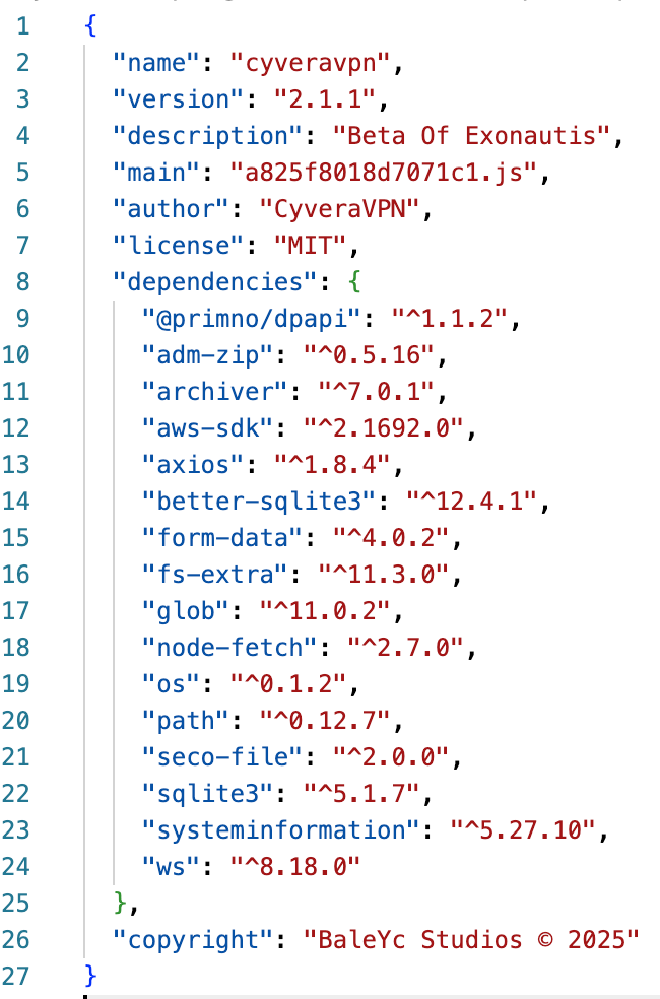
Two things jump out immediately. First, the description says “Beta Of Exonautis” — that’s the lure. Second, the dependency list in this same file reads like a stealer shopping list: @primno/dpapi (Windows credential decryption), better-sqlite3 and sqlite3 (browser database reads), aws-sdk (AWS credential theft), seco-file (Exodus wallet extraction), archiver and adm-zip (data packaging for exfil), ws (WebSocket, used for Chrome DevTools Protocol), systeminformation (system fingerprinting).
No legitimate VPN app needs any of those.
Stage 2: The Loader #
The entry point a825f8018d7071c1.js is a 704KB single-line JavaScript file — no whitespace, no newlines, everything compressed into one long string of code. The first step to understanding it is formatting it with a beautifier, which reveals the obfuscation structure.
| Field | Value |
|---|---|
| Filename | a825f8018d7071c1.js |
| Size | 721,857 bytes (704 KB) |
| SHA256 | fa83180ee18c87e91ab920252e77692e7849b03d8220ace614bd4620bc559bb8 |
| Type | JavaScript — single-line, obfuscated |
The loader uses two obfuscation layers working together.
Layer 1: String table with array rotation. Every string in the code — function names, API calls, file paths, everything — is replaced with an index into a global array called vkAskC[]. Before the code runs, the array gets rotated 9 positions:
function _88259c15(arr, n) {
for (let i = 0; i < n; i++) arr.push(arr.shift());
return arr;
}
const vkAskC = _88259c15([...], 9);
This means static analysis of string indices is meaningless without first applying the rotation. After rotating, every vkAskC[N] resolves to its actual string.
Layer 2: AES-256-CBC encrypted payload. The real malware isn’t in the loader at all — it’s a 639KB base64 blob stored inline. All three decryption parameters (password, salt, IV) are buried in the same array as the blob, just at different indices:
_2b49aac9 = _88259c15([
"d5MFpYl1hx...<639KB blob>...",
"8X9+CehDwyGExpfoGWcausHkyQJp13p+", // password
"8g4EKGu/89SnPfekT4Q8PA==", // salt (base64)
"Er1Dji4aZR4jZUjjIVLA9Q==" // IV (base64)
], 8);
The decryption routine uses PBKDF2-SHA512 with 100,000 iterations to derive the key, then runs standard AES-256-CBC:
const key = crypto.pbkdf2Sync(password, Buffer.from(salt, 'base64'), 100000, 32, 'sha512');
const decipher = crypto.createDecipheriv('aes-256-cbc', key, Buffer.from(iv, 'base64'));
let decrypted = decipher.update(blob, 'base64', 'utf8');
decrypted += decipher.final('utf8');
new Function('require', decrypted)(require);
The last line is the important one: new Function('require', decrypted)(require) — the decrypted payload is executed directly in memory, never written to disk. Classic fileless execution.
Decrypted Parameters
Password: 8X9+CehDwyGExpfoGWcausHkyQJp13p+
Salt: 8g4EKGu/89SnPfekT4Q8PA==
IV: Er1Dji4aZR4jZUjjIVLA9Q==
Derived key: ccd293d10f2251f7508ef6f41c2634db01b94225f33e8113a0c20421b7de558a
Algorithm: AES-256-CBC / PBKDF2-SHA512 / 100,000 iterations
Stage 3: The GenesisStealer Payload #
Decrypting the blob produces a 479KB beautified JavaScript file — the GenesisStealer payload. This is where the actual data theft happens.
Browser Credentials #
The stealer hits every major browser on the machine by reading their SQLite databases directly. Targets include Chrome (across all profiles: Default, Profile 1–5, Guest, Network), Firefox, Brave, Opera GX, Yandex, and Microsoft Edge.
For browsers that are currently running, it goes a step further: it connects to the Chrome DevTools Protocol (CDP) WebSocket endpoint to extract live session cookies from active tabs. This bypasses any cookie encryption, since CDP returns the plaintext values from the running browser process.
Windows DPAPI decryption (via @primno/dpapi) handles the master key needed to decrypt stored Chrome passwords and cookies.
Discord Token Harvesting #
Discord is a primary target. The stealer extracts auth tokens from browser storage, then uses them to query Discord’s API directly:
/api/v9/users/@me— account details/api/v9/users/@me/billing/payment-sources— payment methods and card info/api/v9/users/@me/relationships— friends list/api/v9/users/@me/guilds— server memberships + invite links
The billing endpoint is particularly aggressive — it’s not just account takeover, it’s financial data extraction.
Crypto Wallets #
Two approaches: scan browser extension directories for known wallet extensions, and look for seed.seco files (Exodus wallet seed storage):
path.join(appDataPath, 'seed.seco');
console.log("[WALLET] Recherche des wallets d'extensions..");
The French in that log line — “Recherche des wallets d’extensions” — is interesting. Either the original developer wrote in French or it’s copypasted from somewhere. Either way, it’s in the payload.
AWS Credentials #
The aws-sdk dependency points to ~/.aws/credentials file scraping and environment variable harvesting. Targeting developers and cloud engineers, not just gamers.
System Fingerprint #
Before exfiltrating anything, the stealer collects a full system profile: hardware/OS details via systeminformation, IP geolocation via http://ip-api.com/json/, and WiFi network info (SSID, signal, radio type) via netsh.
Exfiltration #
Stolen data gets zipped and uploaded with a fallback chain — if the primary fails, it tries the next:
- Cloudflare R2 (primary — attacker-controlled storage)
- GoFile.io →
https://api.gofile.io/serversthenhttps://store{N}.gofile.io/uploadFile - tmpfiles.org →
https://tmpfiles.org/api/v1/upload
After a successful upload, the download URL gets POSTed to two Discord webhooks — the attacker’s notification channel:
https://discord[.]com/api/webhooks/1410035164033323029/DlLUhHp0TRyB1xvzeobaPCYP5ehH93734w9AADTDCeazBJ2m-pzJ-1Jb8wLM3BhPT8t1
https://discord[.]com/api/webhooks/1471177394457935995/BzNVHWw2ZLYtaBrbCHf2QY9Snd5UnkeK3LpzYe4r05fLnmi9eAUijaqLWVEgLIov2yf2
Two webhooks suggests either redundancy (in case one gets reported) or two operators watching the same campaign.
The Bigger Picture: One Builder, Several Faces #
This is where it gets interesting from a threat intelligence perspective.
Searching MalwareBazaar for the GenesisStealer family returns a list of droppers that all look different but are actually identical under the hood.
All of them are ~88MB PE32 NSIS installers. All of them share the same imphash: b34f154ec913d2d2c435cbd644e91687. The table below is shows that all GenesisStealer malware found in MalwareBazaar have the same imphash value. Shout out to burger for uploading the samples.
| Filename | Sha256 | Imphash Value |
|---|---|---|
| CyveraVPN Setup 2.1.1.exe | d24dbda069525134f94904f7a16dbf275abcc0c8d7b0b9c065f39d91d3e2dd7a | b34f154ec913d2d2c435cbd644e91687 |
| plugins.exe | a4a882c22c248f95d2e913b5f83badcb0cd247894ee996ccbc15c575785e4788 | b34f154ec913d2d2c435cbd644e91687 |
| HomuHime Setup 2.1.1.exe | 204b8a498705e97af6b7f050646bc3e9bb8609dc1cf8f57b5f7433e12b2e2319 | b34f154ec913d2d2c435cbd644e91687 |
| VBAudio Setup 2.1.1.exe | 422933a922c14907cf70a3b0d1a15ff9c765aa57ffe39656b1fd16a23d2a670b | b34f154ec913d2d2c435cbd644e91687 |
| Stellar_installer Setup 2.1.1.exe | 068dce8acf9157ba95ad04932f1f5bdebc3660d25ff0f002bf0ccfe6294a7ffe | b34f154ec913d2d2c435cbd644e91687 |
| launcherSetup2.1.1.exe | 1b61cc90e7143f97f267c265858d0c0409b69a2ffec6cfed9c2a794981d756b1 | b34f154ec913d2d2c435cbd644e91687 |
| PinkCraftSetup2.1.1.exe | 6e74795b72834e29cb3bdeb09f5cab5afc88492c782a4f5b7f9892971591edc6 | b34f154ec913d2d2c435cbd644e91687 |
| Teste123Game Setup 2.1.1.exe | 401dec3bbc8bd4ce87cc0bb4ac8aedf6f40205b89476fb4b9ba9ebe0b135d459 | b34f154ec913d2d2c435cbd644e91687 |
| VoiceMixer_x64.exe | dbe6483c3fa475ac6ec6cf2b981ec08a5617093568ef1b04575c129013af6908 | b34f154ec913d2d2c435cbd644e91687 |
| advanturelife.exe | 11de285d451f5f2f24fb449364ee836ea599fb0ed7863643aef43ccf888ecc26 | b34f154ec913d2d2c435cbd644e91687 |
| trackord v2.exe | 4ba6866d613d0cbaaf6e586079b3de4ec0f951abb4ebd8c810ea86623242f186 | b34f154ec913d2d2c435cbd644e91687 |
| PinkCraft Setup 2.1.1.exe | 802f9297ee90fab24e1ab18bf74787a03b3e6ddf681677feb066383038a4f188 | b34f154ec913d2d2c435cbd644e91687 |
| WizardXray Setup 2.1.1.exe | d7a86dadc15ebf5cc064a9d9b413093854c25fdb6b06d3710300fcf4ffc79519 | b34f154ec913d2d2c435cbd644e91687 |
| Spine Setup 2.1.1.exe | 56eb6afd322ef89de23aac3f5b7247a8d0f0b2db508285967e1de242e6050af6 | b34f154ec913d2d2c435cbd644e91687 |
| WizardXray Setup 2.1.1.exe | 4e25306a7912045b5806be298d0e23de4153e331b0793b446fb123d77f072ccc | b34f154ec913d2d2c435cbd644e91687 |
| RPReplaysextapeleak3_12_2025_exclusifleak2025.mp4.exe | b9d0951bbd62ad86da613fa3fcb939228305094bdc4462d06f8fd3f57e7a9b63 | b34f154ec913d2d2c435cbd644e91687 |
| Rooted Setup 2.1.1.exe | 1715bffc46bace588a5015bcc089fcad4d9905d6c7ed8a51c4d2ff970f3fe692 | b34f154ec913d2d2c435cbd644e91687 |
| Loder Setup 2.1.1.exe | 86999ec14bdd085e1ec3acea4620d971369b928337f29169c941ffce276bf1c9 | b34f154ec913d2d2c435cbd644e91687 |
| vrchat Setup 2.1.1.exe | 38a03d16be9da16695e2a286948482e2fd9ca8f303213a8f6ba1ab10627fea8c | b34f154ec913d2d2c435cbd644e91687 |
| Everlight Setup 2.1.1.exe | 33b01253db889904fe50103771ff248d6c836098917b20554cc5bce967be7c9b | b34f154ec913d2d2c435cbd644e91687 |
| RPReplaySextapeleak13-2025-onlyfansleakfullvids.mp4.exe | 0a05c686d8661d0abbfde1b9619848b9041a63b7dcaf2ec36623fb5f5b811856 | b34f154ec913d2d2c435cbd644e91687 |
| ArenaWarsSetup.exe | 82df15c58bd8eccbc4c8c9e443a1a57c4f70189745f6799a73ddecc3315910cd | b34f154ec913d2d2c435cbd644e91687 |
| RPReplaySextapeleak2025_onlyfansleakfullvids.mp4 Setup 2.1.1.exe | a0c26a10466c6c8e6b92e4adc85cc99a970bb4d903b60adf5c1499e9b094d7b0 | b34f154ec913d2d2c435cbd644e91687 |
| MuckModLoader Setup 2.1.1.exe | ef591a22899653a15acd0c3f303d8659d7022df02681148891dcd153a8a5a317 | b34f154ec913d2d2c435cbd644e91687 |
| RPReplaySextapeleak2025_mymleakfullvid.mp4 Setup 2.1.1.exe | 9ffc66cfdbe4780957925370962a69757cb000b30e7dfa5788f160670364a326 | b34f154ec913d2d2c435cbd644e91687 |
| RPReplaySextapeleak2025_mymleakfullvid.mp4 Setup 2.1.1.exe | 3930988ec97fe425cf4441f22dc4dca0aa086b3c7100ee2f67e13fe80b804151 | b34f154ec913d2d2c435cbd644e91687 |
| ZarvethisSetup.exe | 88faf2ec9c45158188a6ef03e15e1f0f7d575a365d6bd9ea7e5cf49cb001e5e2 | b34f154ec913d2d2c435cbd644e91687 |
| Xeno.exe | 72eb5b258772910e96a77d3b112fdb30e34013255b062f0a1cdaff6c2d204b0c | b34f154ec913d2d2c435cbd644e91687 |
| output.exe | 944b2b3fc5d769e1edd6d9f0790692fa45adbee43d2d1687792246e7e84f3f63 | 1d8915c3554f512929a8d501df563d33 |
| panel.exe | 50a362c59eac4bd2d6c3e211f3cdd661653f49d5050806f698949c7211ac6a7b | 4d0fb8dc9ee470058274f448bebbb85f |
| panel.exe | 769c32ff651161a57d38891ad1a8c331b8fbf21aeadc84008cef9793c6afa9d3 | 4d0fb8dc9ee470058274f448bebbb85f |
| loader Setup 1.0.0.exe | 8371908f5e73cb72d7cfe1b7f5e6067fc1be0faa2bf57595f71f8e9494d05381 | b34f154ec913d2d2c435cbd644e91687 |
| loader Setup 1.0.0.exe | 82e81546a33347df0a2597520effe148bc951c289b7cd42b24cd157f457da8eb | b34f154ec913d2d2c435cbd644e91687 |
| KalyLauncher Setup 1.0.0.exe | 24c0ba6060643f5428f88a293ff4ee911bc1a3cb06e077468b3042b7700537f0 | b34f154ec913d2d2c435cbd644e91687 |
| ToolV4 Setup 1.0.0.exe | cf491a017db7d3182b918b0aad98b52ed0bcff6df384e9ba3d291c5aecbc93f4 | b34f154ec913d2d2c435cbd644e91687 |
What is imphash? #
It’s an MD5 hash computed from a PE file’s import table — the ordered list of DLLs and functions the binary imports. Think of it as a fingerprint of how a program was compiled and linked, independent of what payload it carries. Two executables built from the same source code with the same dependencies will share an imphash even if their contents differ completely.
This matters because it means the actor can swap lure names, embed different payloads, and repackage the installer as many times as they want — but the imphash stays the same until they rewrite the builder. That’s a clusterable, pivotable indicator that survives all the cosmetic changes.
The 2.1.1 version string is another leak. It appears hardcoded across most dropper names and in package.json — it’s the builder version, not the impersonated software’s version number. The actor forgot (or didn’t care) to strip it.
The lure strategy is targeted: fake games, fake audio tools, fake launchers — all things that circulate in Discord servers and gaming communities. This is intentional. Discord tokens, gaming accounts, and crypto wallets are the primary targets, and these lures reach the right victims.
IOCs #
File Hashes (Sha256) #
d24dbda069525134f94904f7a16dbf275abcc0c8d7b0b9c065f39d91d3e2dd7a CyveraVPN Setup 2.1.1.exe (NSIS dropper)
fa83180ee18c87e91ab920252e77692e7849b03d8220ace614bd4620bc559bb8 a825f8018d7071c1.js (JS stealer payload)
URLs #
https://discord[.]com/api/webhooks/1410035164033323029/DlLUhHp0TRyB1xvzeobaPCYP5ehH93734w9AADTDCeazBJ2m-pzJ-1Jb8wLM3BhPT8t1 Discord Webhook
https://discord[.]com/api/webhooks/1471177394457935995/BzNVHWw2ZLYtaBrbCHf2QY9Snd5UnkeK3LpzYe4r05fLnmi9eAUijaqLWVEgLIov2yf2 Discord Webhook
